Mobile Hacking Lab - Food Store Writeup

Hello, in today’s writeup, I will walk you through Food Store lab MobileHackingLab.
In this lab we will exploit SQL Injection vulnerability to in sign up to get access to pro account.
To understand what is SQL Injection, you can see this tutorial and to learn how to do android pentesting and learn tools, you can see this.
So, let’s download the APK file and open it in an Android emulator.
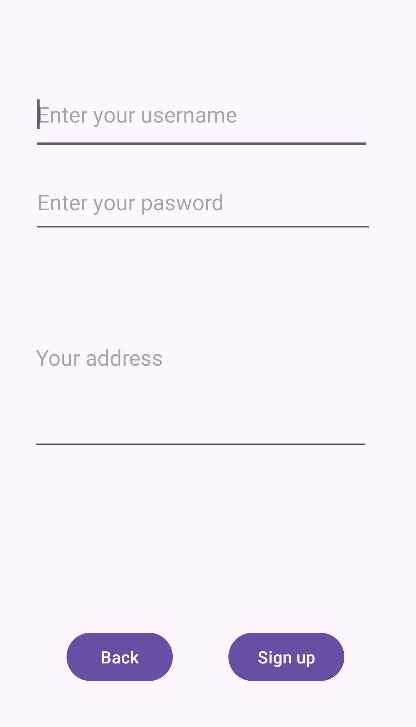
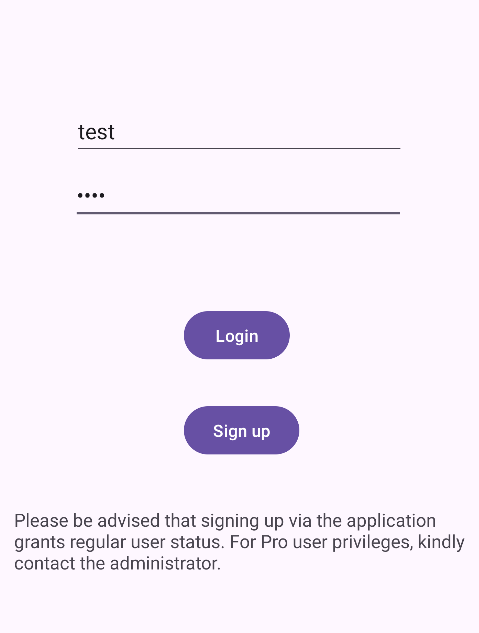
We can see signup and login pages, so let’s create an account and log in using test:test.
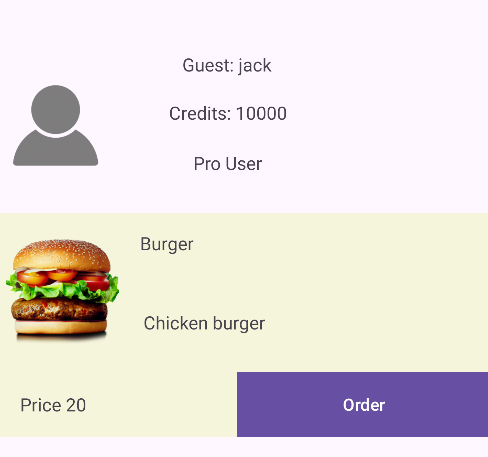
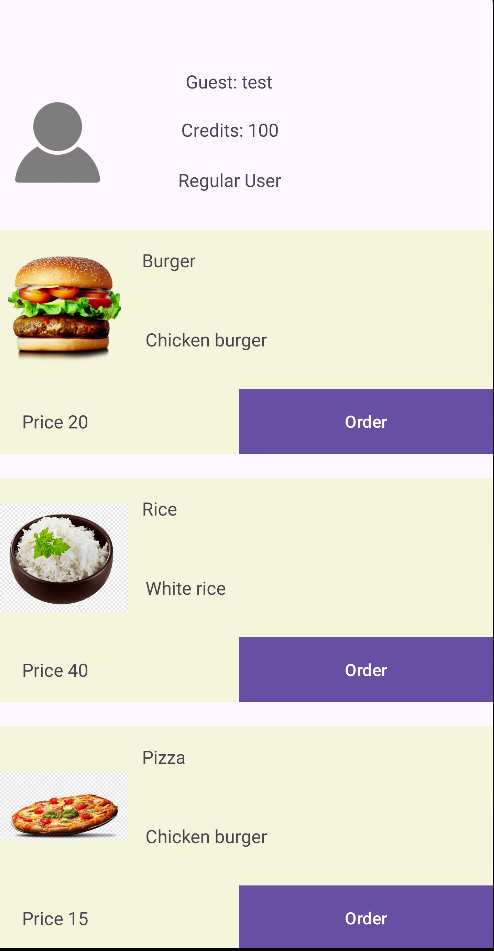
The app redirects us to the dashboard, which contains some foods to order, and we are in Regular User mode.
As we explore the app at runtime, let’s analyze it using JADX-GUI.
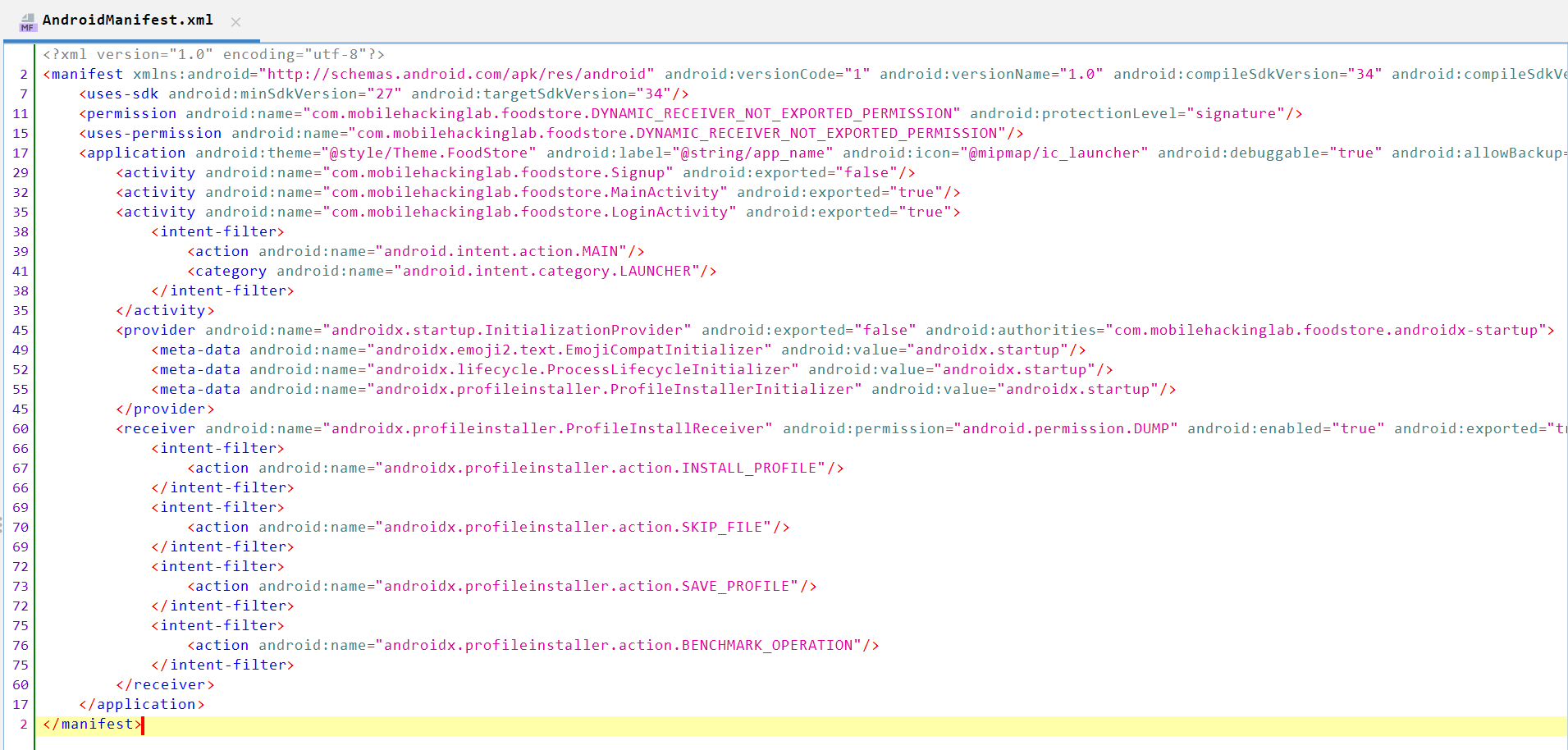
AndroidManifest.xml contains three activities which we saw earlier: Signup, LoginActivity, and MainActivity.
Let’s start with LoginActivity as it is the LAUNCHER of the application.
We can see it first defines dbHelper and calls the database.
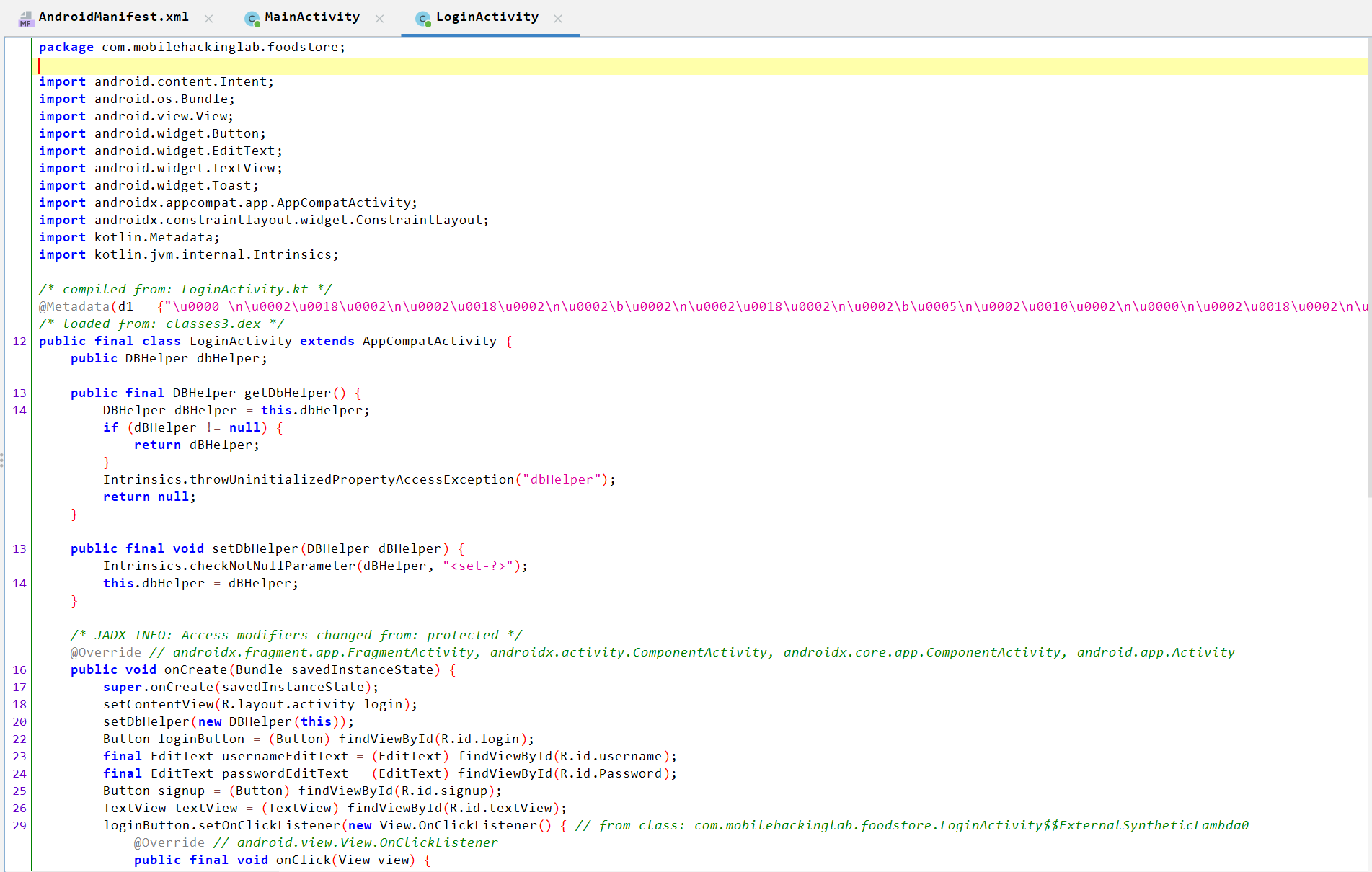
Note that if we become a pro user, the credits become 10000 instead of 100.

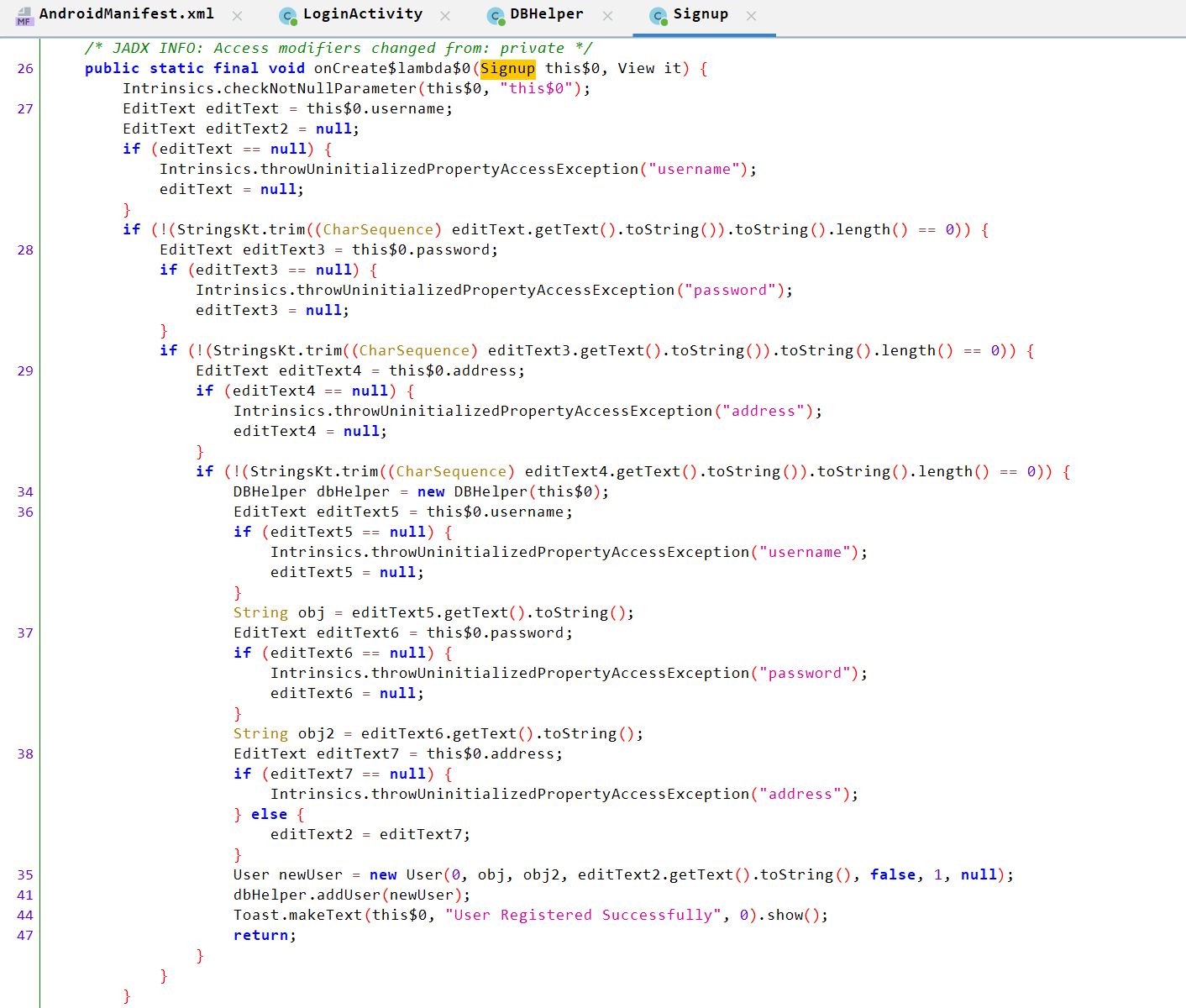
The Signup activity takes username, password, and address from user inputs, checks they are not empty, then passes them to DBHelper.adduser().
A DBHelper instance is created to save the user to the database.
Let’s move to DBHelper to analyze the database behavior.
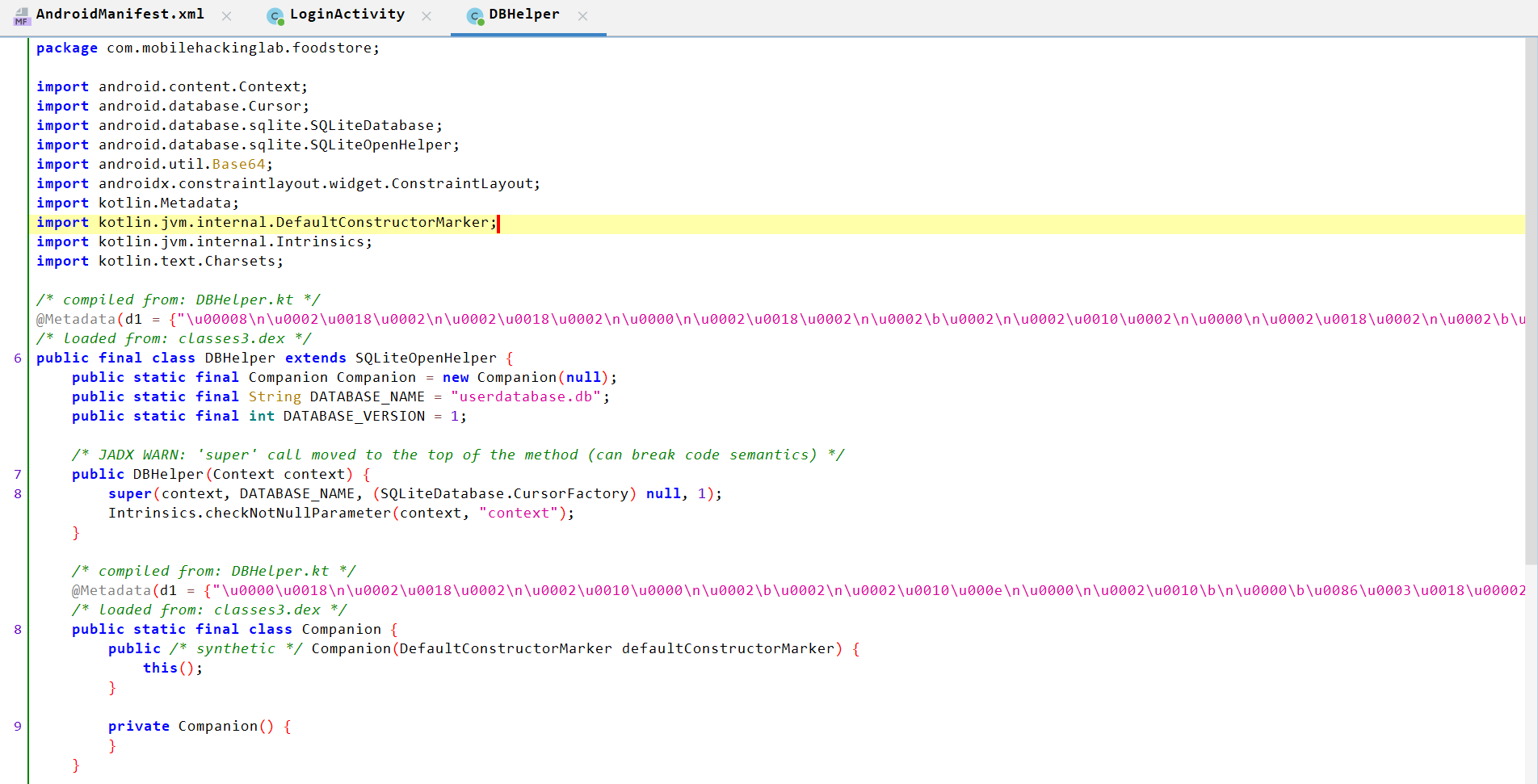
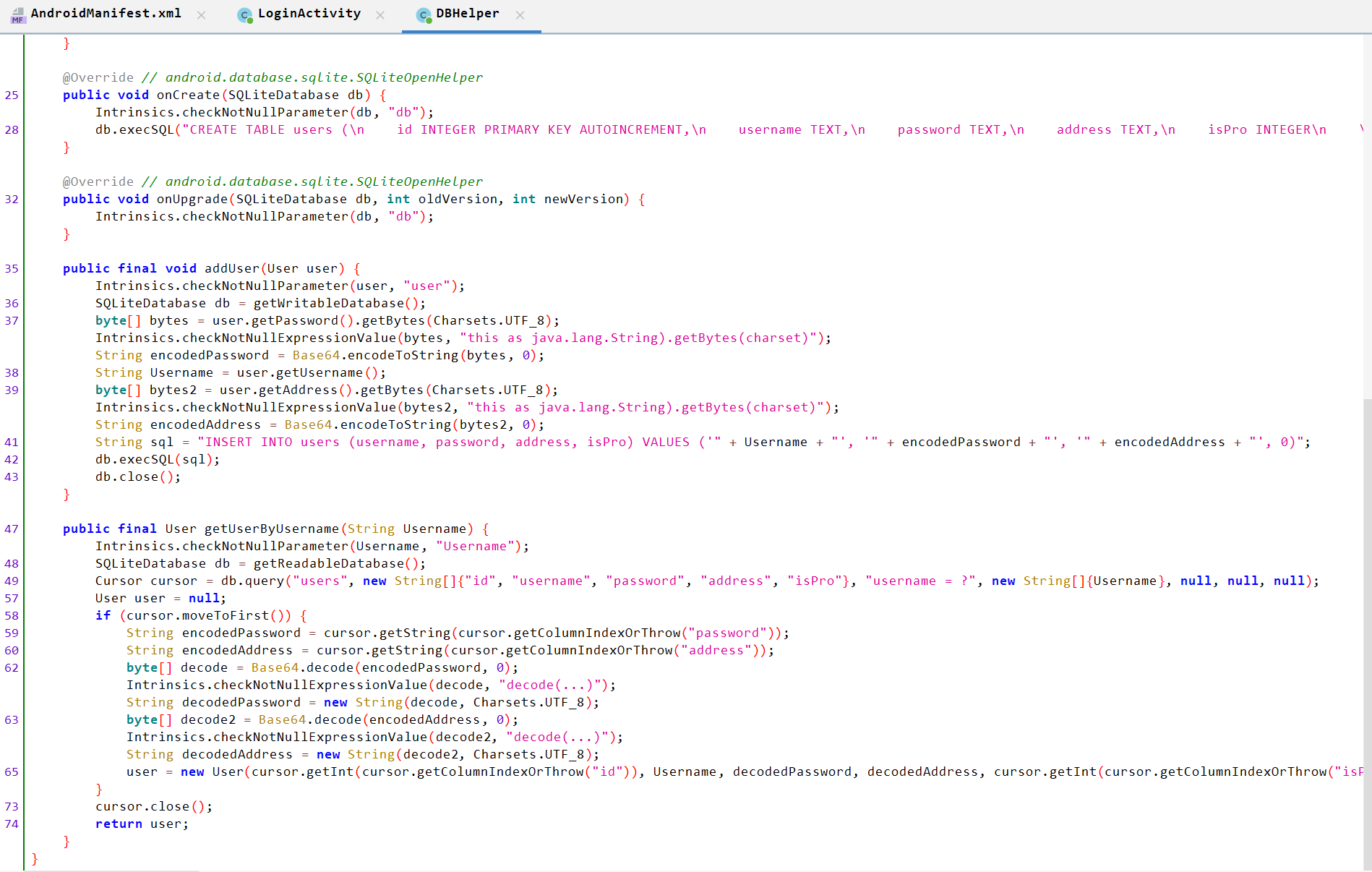
DBHelper Analysis:
- Creates the
userdatabase.dbdatabase, which can be found in/data/data/<package_name>/databases/. - Creates the
userstable and defines the following columns:idusernamepasswordaddressisPro
- Inserts data into the
userstable;isProis assigned0by default. The stored data format is:- Username in plain string format
- Base64-encoded password
- Base64-encoded address
- Retrieves user data using
getUserByUsername- The
getReadableDatabase()method opens a connection to the database with read-only permissions. - Decodes the password and address
- Returns the record according to user id.
- The
We can see that user-controlled data is inserted into the database without validation or sanitization.
Therefore, we can manipulate the SQL query and perform SQL Injection to become a pro user.
SQL Query:
insert INTO users (username, password, address, isPro) Values (' " + username + "', ' " + encodedPassword + "', ' " + encodedAddress + "', 0)
We need to inject a payload during signup that allows us to become pro. We can use the following SQL injection payload:
jack','amFjaw==','amFjaw==',1); --
Explanation:
jackis the username.amFjaw==is the base64-encoded password and address, which decodes tojack.1is theisProvalue.
Then we can add random values in the password and address fields.
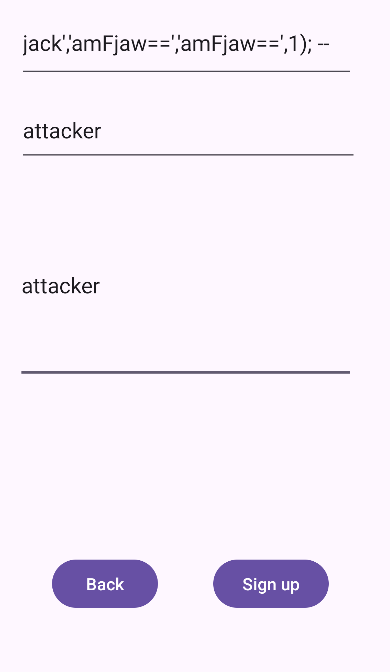
If we log in with jack:jack, we will be redirected to the dashboard and become a Pro User.